В Саратов приехала съемочная группа фильма о "Комбинации"
14:34, 26.04.2024
В Саратов прибыла съемочная группа кинокомпании "Лунапарк", которая снимает многосерийный художественный фильм о группе "Комбинация", рассказал зампред правительства региона Михаил Орлов в соцсетях. С директором картины Михаилом Формихиным помимо Орлова встретились министр культуры Наталия Щелканова, члены региональной кинокомиссии и представители мэрии. Съемочный процесс в Саратове должен начаться 21 мая. "Но предварительная работа съемочной группы совместно с министерством......
S7 Airlines будет выполнять рейсы из Новосибирска в Астану
14:34, 26.04.2024
26 апреля 2024, 09:35, Travel.ru - Авиакомпания S7 Airlines начала продавать билеты на прямые регулярные рейсы между Новосибирском и Астаной. Первый перелет между главный городом Новосибирской области и столицей Республики Казахстан должен состояться 24 мая 2024 года. Полеты запланированы 2 раза в неделю – по понедельникам и пятницам. Самолет будет отправляться из новосибирского аэропорта Толмачево в 15:30 по местному времени и прибывать в Астану в 15:30. Обратный рейс из столицы Казахстана назначен на 16:35, прибытие в российский аэропорт – в 20:20 с учетом разницы во времени. Всего во время перелета пассажиры проведут в воздухе около 2 часов. Билеты на эти рейсы можно купить на официальном портале авиакомпании, в собственном мобильном приложении S7 Airlines и у агентов. Сейчас, например, можно приобрести билеты на июнь туда и обратно по наиболее бюджетному тарифу "Эконом Базовый" по цене примерно 15000 рулей: за эту стоимость без дополнительной оплаты с собой можно взять одно...
Из Нижнего Новгорода пойдут "Метеоры" в Ульяновск и Рыбинск
14:34, 26.04.2024
26 апреля 2024, 08:35, Travel.ru - В период летней речной навигации 2024 года будет запущено несколько новых маршрутов из Нижнего Новгорода, которые будут интересны не только местным жителям, но и туристам: "Метеоры" пойдут в Ульяновск и Рыбинск, начнут совершаться рейсы в Дзержинск, также будет увеличена частота рейсов в Балахну и Городец – они будут выполняться трижды в день, сообщает туристический Telegram-канал @dearpassengers со ссылкой на компанию-оператора речных маршрутов "Водолет". Из Нижнего Новгорода в Ульяновск пассажиров будут перевозить быстроходные суда "Метеор 120Р". На маршруте будут сделаны остановки в Козьмодемьянске, Чебоксарах и Казани. Рейсы запланированы 3 раза в неделю. Из Нижнего Новгорода корабль будет отправляться по вторникам, четвергам и субботам в 06:00 утра по местному времени, из Ульяновска – по средам, пятницам и воскресеньям. В конце мая появится также расписание дополнительных рейсов до Казани. Судно из Нижнего Новгорода до Рыбинска будет след...
Былина «Садко»: характеристика главных героев произведения
14:34, 26.04.2024
Цикл былин «Садко» был записан фольклористами в Олонецкой губернии в нескольких вариациях....
Три музы Игоря Ливанова: о личной жизни актера
14:34, 26.04.2024
Красавец в жизни и на экране Игорь Ливанов своей игрой, умением эффектно появиться в кадре снискал любовь женской половины публики....
Психологические состояния человеческой личности
14:34, 26.04.2024
Безусловно, человек является весьма сложно устроенным существом. Психологические состояния человека могут выявляться в самых разных проявлениях. В данной статье рассмотрены лишь несколько психологических состояний человека. Состояние обеспокоенности Состояние обеспокоенности сопровождается нестабильностью эмоционального состояния. Другими словами, состояние человека является неуправляемым. Человек не в силах контролировать свои эмоции, свои вербальные и невербальные проявления. У некоторых людей получается в какой-то степени воздействовать на свою вербальную и невербальную речь, однако данный контроль все равно остается лишь попыткой и не достигает поставленной задачи в должной мере. Состояние обиды Само по себе состояние обиды является проявлением отрицательного состояния. Обида несет в себе зачастую деструктивную составляющую. Человек, находящийся в состоянии обиды, наносит реальный вред лишь себе. Состояние обиды весьма сильно сказывается на эмоциональном состоянии человека. Следует...
Андрогенная алопеция
14:34, 26.04.2024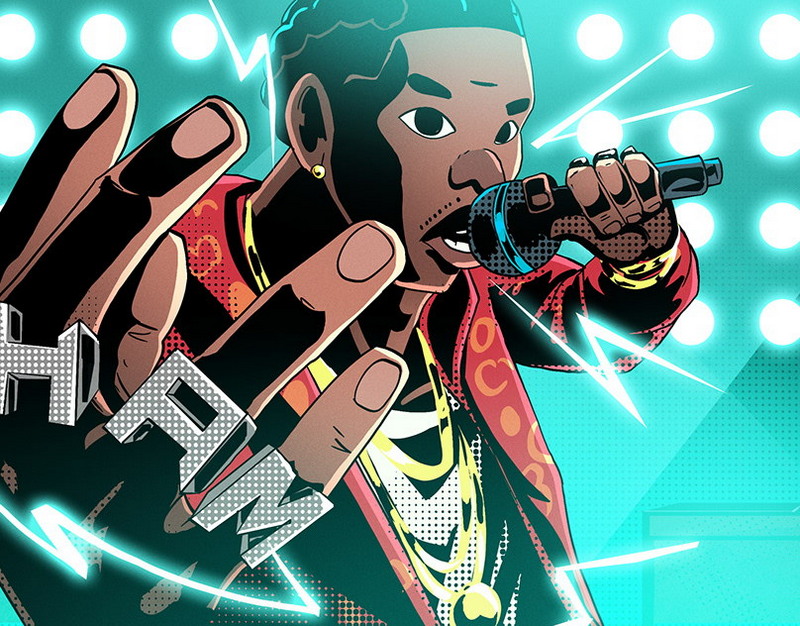
Безвозвратное выпадение волос, к сожалению, явление не столь редкое. В большей степени ему подвержены мужчины, но в последние годы данные официальной статистики указывают на то, что процент женщин с подобным синдромом значительно вырос. Почему это происходит? Существует множество причин, почему волосы начинают активно выпадать, а на их месте не вырастают новые, как это случается при естественном отмирании волоса. Самое большое распространение эта проблема получила среди женщин, которые стали мамами. Причем видимый эффект может наступить через год или два после рождения ребенка. В таких случаях врачи – трихологи ставят диагноз, в основе которого лежит активное воздействие на структуру волоса дигидротестостерона или иначе — биологически активной формы мужского полового гормона тестостерона. В послеродовой период гормональный баланс женщины находится в состоянии полного хаоса, на фоне которого очень быстро развивается андрогенная алопеция. Существуют и другие причины возникновения с...
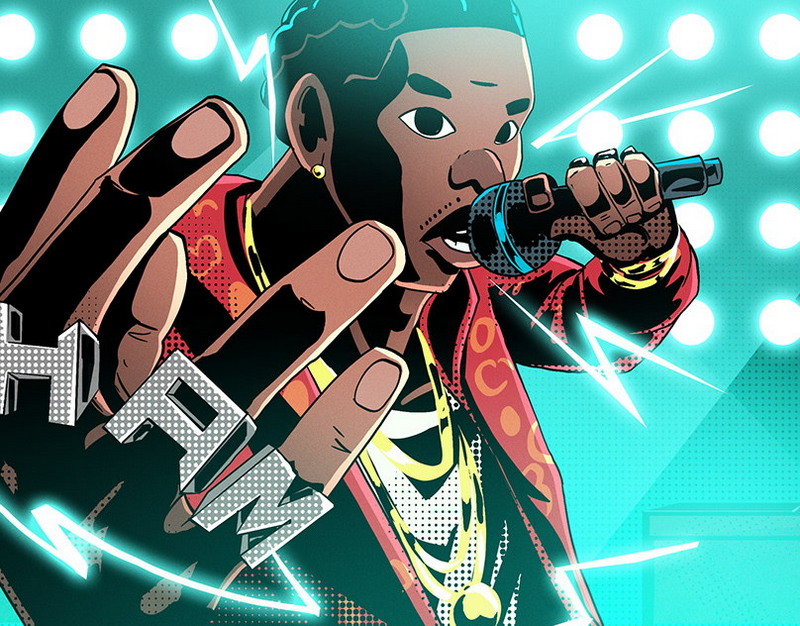
Состоялась премьера нового хита Данко
14:34, 26.04.2024
Исполнитель Данко презентовал новый трек — вышла в свет песня «Берег Рай». Певец посвятил песню древнегреческой богине Афродите. С его слов этот дар богиня приняла и указала людям путь к тому самому долгожданному берегу. Как пишет портал «Новости Букинг 90-х», этот трек в коллаборации с Cubetonic может стать одним из самых популярных у исполнителя. Что же покорит слушателя? Мелодичность, звучность, а также безусловно красивый текст с глубоким смыслом. Что ж, кажется, этот релиз станет настоящим хитом на радио и в социальных сетях, как и ранние хиты Данко. Данко – псевдоним исполнителя Александра Фадеева. Его первый альбом вышел в 2000 году и сразу же попал во все хит-парады страны. Данко сотрудничал с такими исполнителями как Игорь Бутман, Ла Камилла, Паштет, Маша Кац. Ранее Москва.ру рассказала о том, что мэр Москвы Сергей Собянин отчитался о том, что Москва стала в два раза ярче, чем была 12 лет назад. Сейчас город освещают более одного млн уличных ламп и фонарей.The post Состоялас...
Скончался сценарист фильма «Белые росы» Алексей Дударев
14:34, 26.04.2024
В Белоруссии скончался известный белорусский деятель культуры Алексей Дударев. Автор сценария культового фильма «Белые росы» и пьесы «Рядовые» ушел из жизни во возрасте 72 лет. Ушел из жизни легендарный белорусский сценарист и драматург, лауреат Государственной премии СССР, заслуженный деятель искусств Республики Беларусь, председатель Белорусского союз театральных деятелей Алексей Ануфриевич Дударев. Об этом сообщает РИА Новости со ссылкой на заявление министерства культуры Белоруссии. В заявлении отмечается, что Дударев внес значительный личный вклад в развитие и популяризацию белорусского национального театрального искусства. Ранее Москва.ру сообщала о том, что в Москве 3 марта состоится церемония прощания с Глебом Павловским. Прощание с журналистом и политологом Глебом Павловским состоится 3 марта в 11 часов в траурном зале ЦКБ.The post Скончался сценарист фильма «Белые росы» Алексей Дударев first appeared on Москва.ру....
Со слезами на глазах
14:34, 26.04.2024
Доживи дед до наших дней, мог бы увидеть парад Победы и шествие «Бессмертного полка» в родном Ельце. Но в прошлом году парад в Ельце отменили, как и в 22 других городах России.Из соображений безопасности, разумеется. Ну, с приграничными регионами понятно, прилетает туда регулярно. Непонятно, почему следом в «отказ» пошли Сургут, Ханты-Мансийск, Нижневартовск, Тюмень, до которых тысячи километров… Хотя вот уже сейчас беспилотники со смертельной начинкой атаковали Елабугу и Нижнекамск в Татарстане, преодолев более 1200 км от украинской границы. Поговаривают, что скоро и в Сибирь полетят.На днях девять регионов объявили, что решили не проводить парады Победы, и, несомненно, ближе к 9 мая их будет еще больше. Безопасность прежде всего. Первый зампред комитета ГД по международным делам Светлана Журова так и сказала: «Здесь каждый субъект сам ориентируется на ситуацию. Главное – безопасность. Особенно в приграничных регионах [не стоит] провоцировать ту сторону что-то сделать, побомбить или р...
ПАСЕ посеяла ветер
14:34, 26.04.2024
В резолюции 29 пунктов, есть среди них и такой: «Ассамблея не признает легитимность Владимира Путина в качестве президента РФ и повторяет свой призыв к государствам – членам Совета Европы и государствам-наблюдателям, а также Европейскому союзу прекратить все контакты с ним, за исключением гуманитарных целей и стремления к миру». Будет ли это решение иметь какие-либо юридические и иные последствия? Об этом «Собеседник» спросил у доктора юридических наук, профессора кафедры международного права, главного научного сотрудника лаборатории международно-правовых исследований МГИМО МИД РФ Дмитрия Лабина:– Вопрос по делу: нет, никаких юридических или других последствий эта резолюция иметь не будет. Пусть не смущает россиян солидная аббревиатура ПАСЕ, подобные международные организации – это не законодательные или судебные органы, которым мы бы подчинялись, и вообще они не вправе давать какое-либо суждение по поводу суверенных государств. Потому что современный миропорядок определяет Устав ООН,...